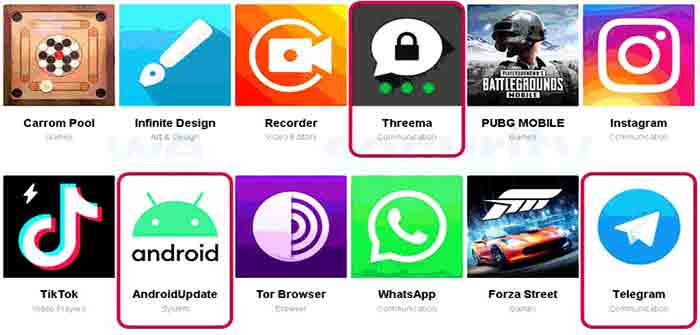
A hacking group known for its attacks in the Middle East, at least since 2017, has recently been found impersonating legitimate messaging apps such as Telegram and Threema to infect Android devices with a new, previously undocumented malware.
“Compared to the versions documented in 2017, Android/SpyC23.A has extended spying functionality, including reading notifications from messaging apps, call recording and screen recording, and new stealth features, such as dismissing notifications from built-in Android security apps,” cybersecurity firm ESET said in a Wednesday analysis.
First detailed by Qihoo 360 in 2017 under the moniker Two-tailed Scorpion (aka APT-C-23 or Desert Scorpion), the mobile malware has been deemed “surveillanceware” for its abilities to spy on the devices of targeted individuals, exfiltrating call logs, contacts, location, messages, photos, and other sensitive documents in the process.
In 2018, Symantec discovered a newer variant of the campaign that employed a malicious media player as a lure to grab information from the device and trick victims into installing additional malware.
Then earlier this year, Check Point Research detailed fresh signs of APT-C-23 activity when Hamas operators posed as young teenage girls on Facebook, Instagram, and Telegram to lure Israeli soldiers into installing malware-infected apps on their phones…
Continue Reading